Category: PC & Tech
-

Steam will not support Ubuntu 19.10 and later over 32-bit compatibility
Valve has officially announced that it is dropping support for Ubuntu 19.10 and future releases, due to latter’s decision to stop providing 32-bit packages in its archives.
-

How to Convert Videos to Audio Files?
In this article, we will talk about different methods and tools that you can use to convert videos to audio files.
-

10 Tech Must-Haves for the Aspiring Professional Gamer
Are you an aspiring professional gamer? As you work on perfecting your kill shot strategy and reaction times, revamp your rig with these 10 tech must-haves.
-

Desktop Alert System For Critical Information Delivery
A great way to get your information to them is by investing in a desktop news ticker – a small window of moving text that scrolls along the bottom of their computer screens.
-

WhatsApp call exploit left Android phones and iPhones vulnerable to Israeli spyware
Whatsapp has disclosed a vulnerability that allowed hackers to remotely install spyware on iOS and Android phones by exploiting a bug in the audio call feature of the app.
-

Steam Link Anywhere beta will allow you to play your PC games wherever you like
Valve has introduced Steam Link Anywhere service that allows users to play games from their personal library on a client device outside of your local network.
-

3 Big Reasons Why You Need a Cloud-Based Quality Management Solution
If you are not utilizing the cloud for your quality management solution then here are 3 big reasons why you need a cloud-based quality management solution.
-

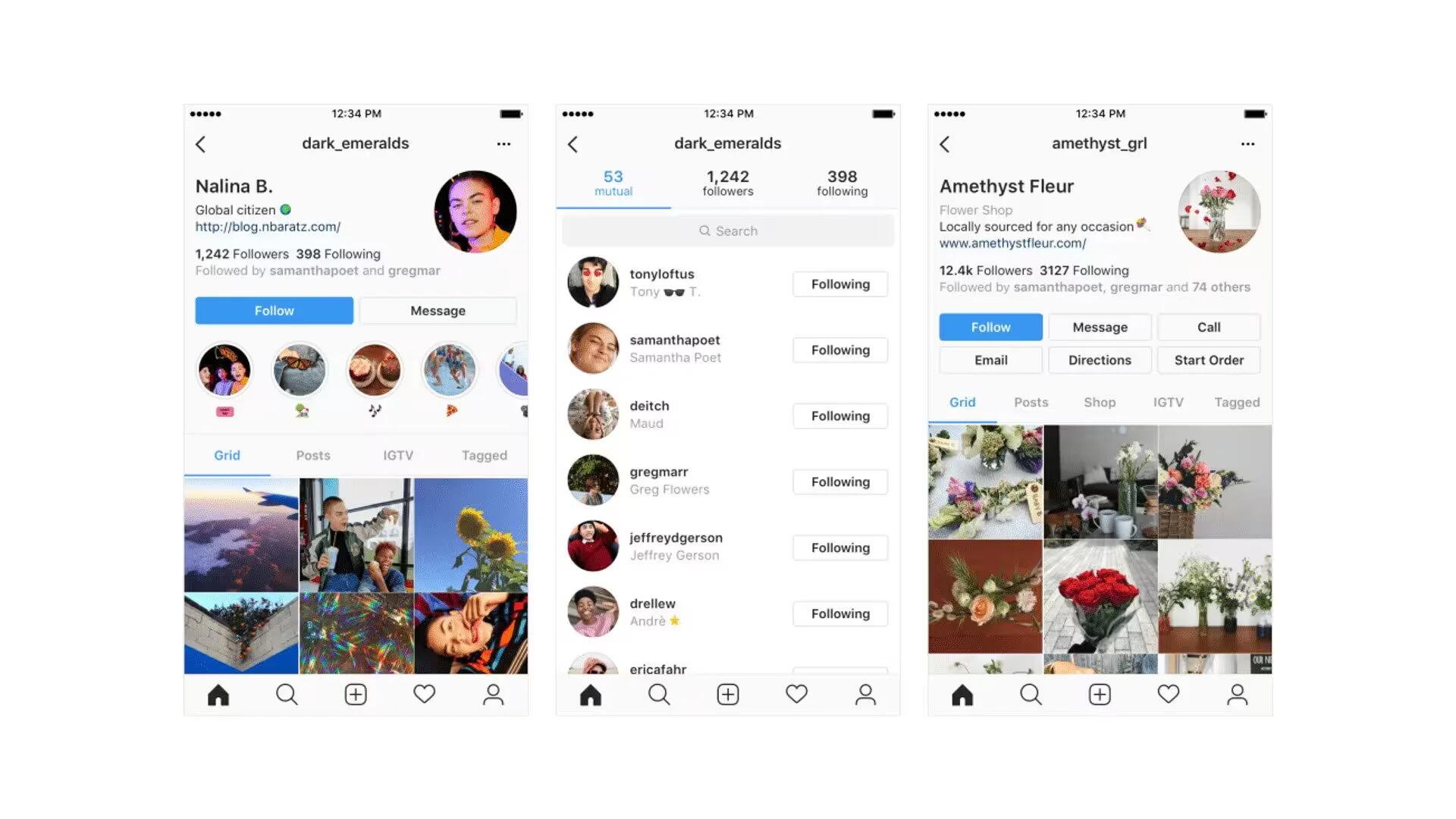
New Facebook bug exposes up to 6.8 million users’ private photos to app developers
Today, Facebook disclosed a bug in their Photo API that gave app developers access to the photos of up to 6.8 million users.
-
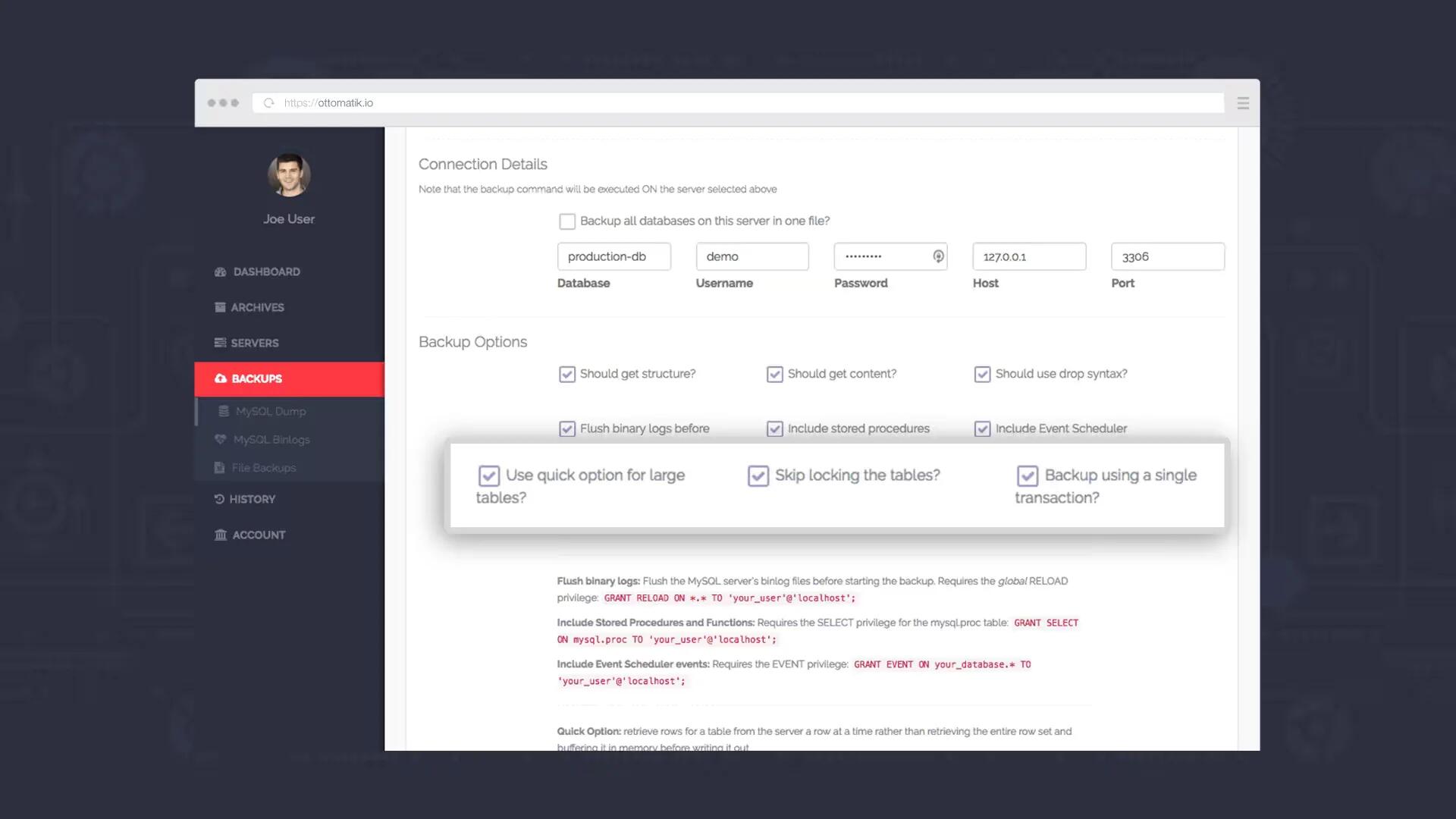
Learn More about MySQL Backup with Ottomatik
In this piece, you can educate yourself on the functions of MySQL backup applications that are useful in data management.
-
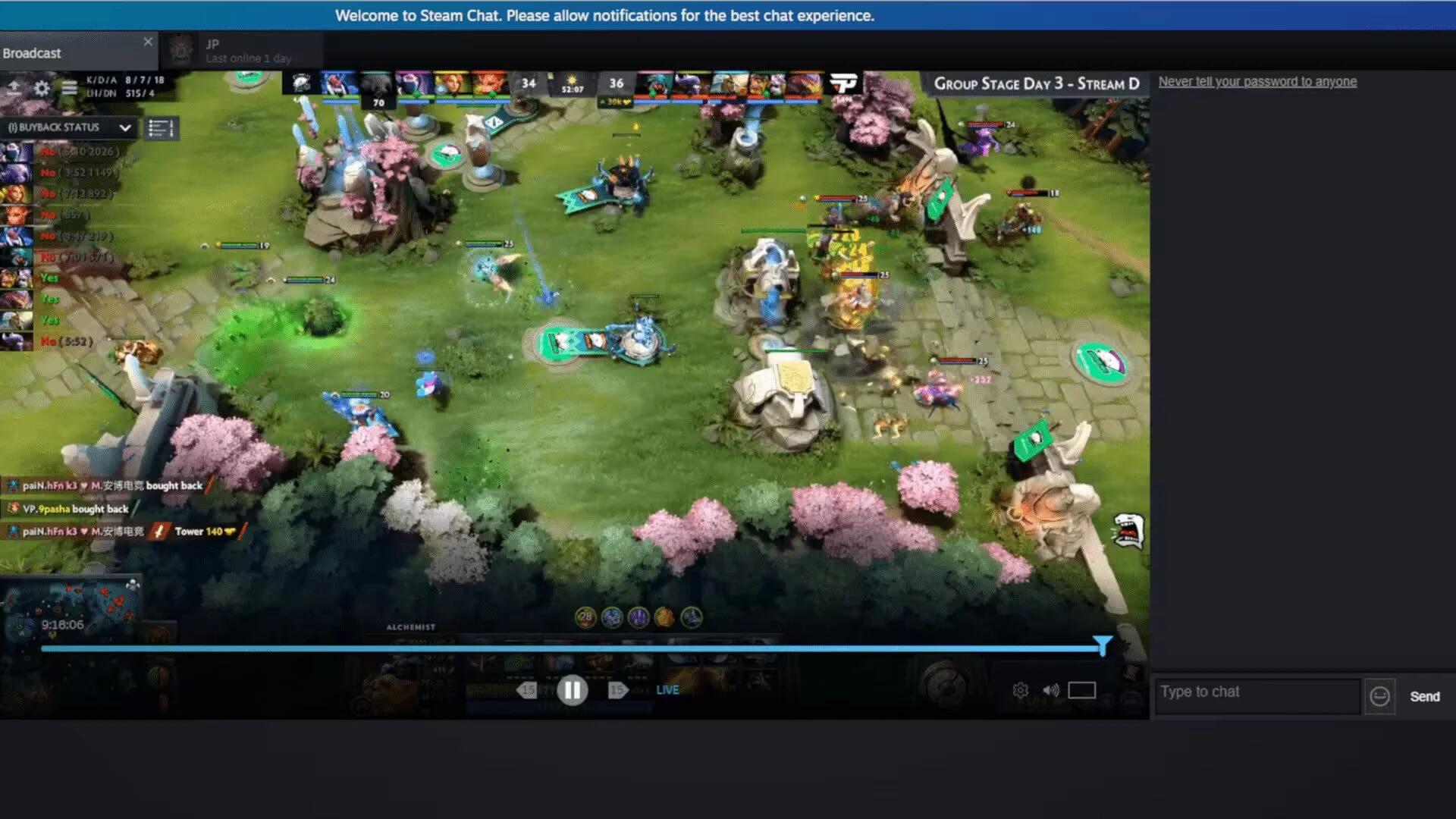
Valve accidentally reveals Steam.TV – a competitor to Twitch live streaming platform
This Friday, Valve has accidentally debuted a Twitch-like live streaming platform called Steam TV, showcasing a stream from Valve’s own annual Dota 2 tournament, The International 2018.
-
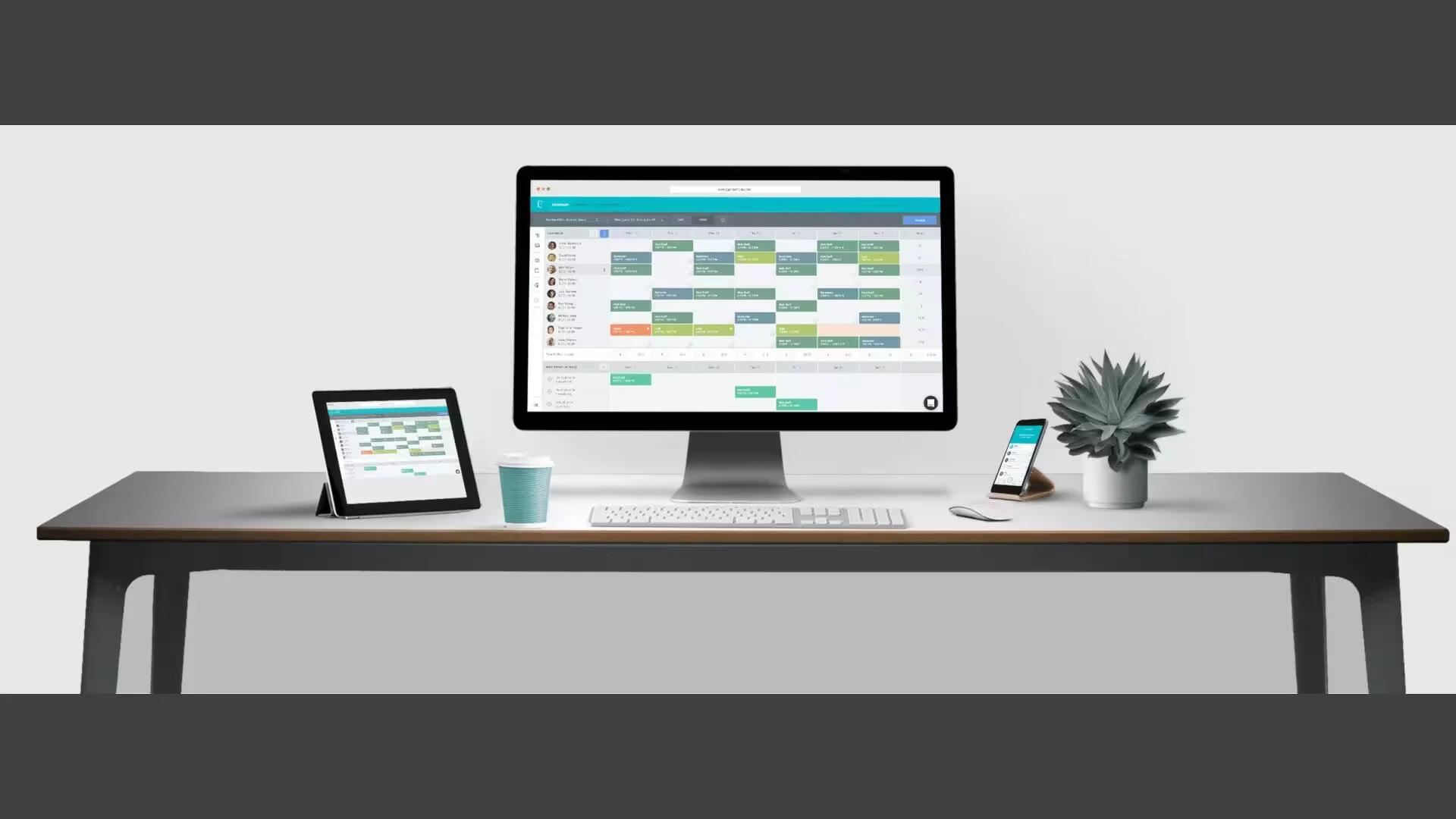
How can an Attendance Management System help business owners and their employees?
Here is how an Attendance Management System (or Time and Attendance software) can help business owners by allowing employees to manually clock in and out of shifts.
-

Samsung Galaxy S10 will reportedly come in three different sizes
According to a recent report from TF International analyst Ming-Chi Kuo, Samsung is gearing to launch the Galaxy S10 in three different screen sizes in 2019.
-

HTC records lowest monthly revenue in two years, despite the U12+ launch
It looks like HTC is in trouble as the Taiwanese smartphone maker revealed a 68 percent drop in sales for the month of June.
-

Act like a Roku Master with these simple tricks
In this blog, you will get to know all the latest features of Roku Streaming Stick device and how to use them to like a pro.
-
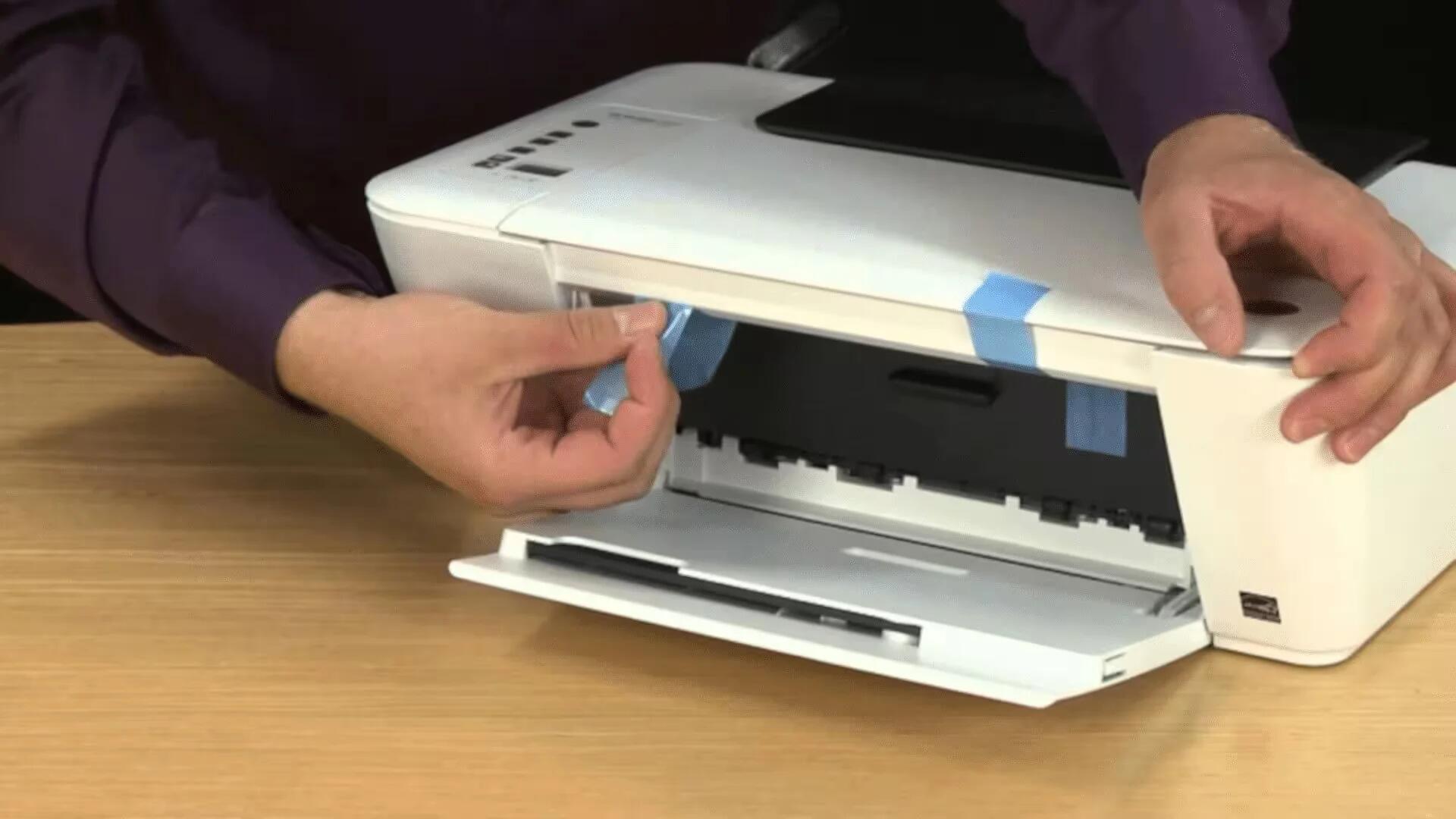
Tips and Tricks to Secure your Wireless HP Printer
Sometimes your wireless Printer is leaving a gaping hole for hackers and here are some tips and tricks to protect your wireless HP Printer.
-

Pandora introduces a new unlimited family plan for $15 per month
Pandora has launched a new family plan with unlimited streaming for $14.99 a month, matching the price of Apple Music and Spotify.
-

Infographic – PayPal’s journey to the biggest online payment system in the world
The prominent success story of PayPal has inspired many start-ups. The following infographic will show PayPal’s success story on becoming world’s largest online payment system.