Category: PC & Tech
-

Innovative Apps for Improving Writing and Research in Essay Writing
It may be worth trying using technology to solve your writing and research issues, and here is a list of innovative apps for improving writing and research in essay writing.
-

5 Ways New AI Programs Are Revolutionizing the Way We Browse
Artificial Intelligence (AI) has drastically changed the way people use the internet, and here are five ways the AI programs are revolutionizing how people browse the web.
-
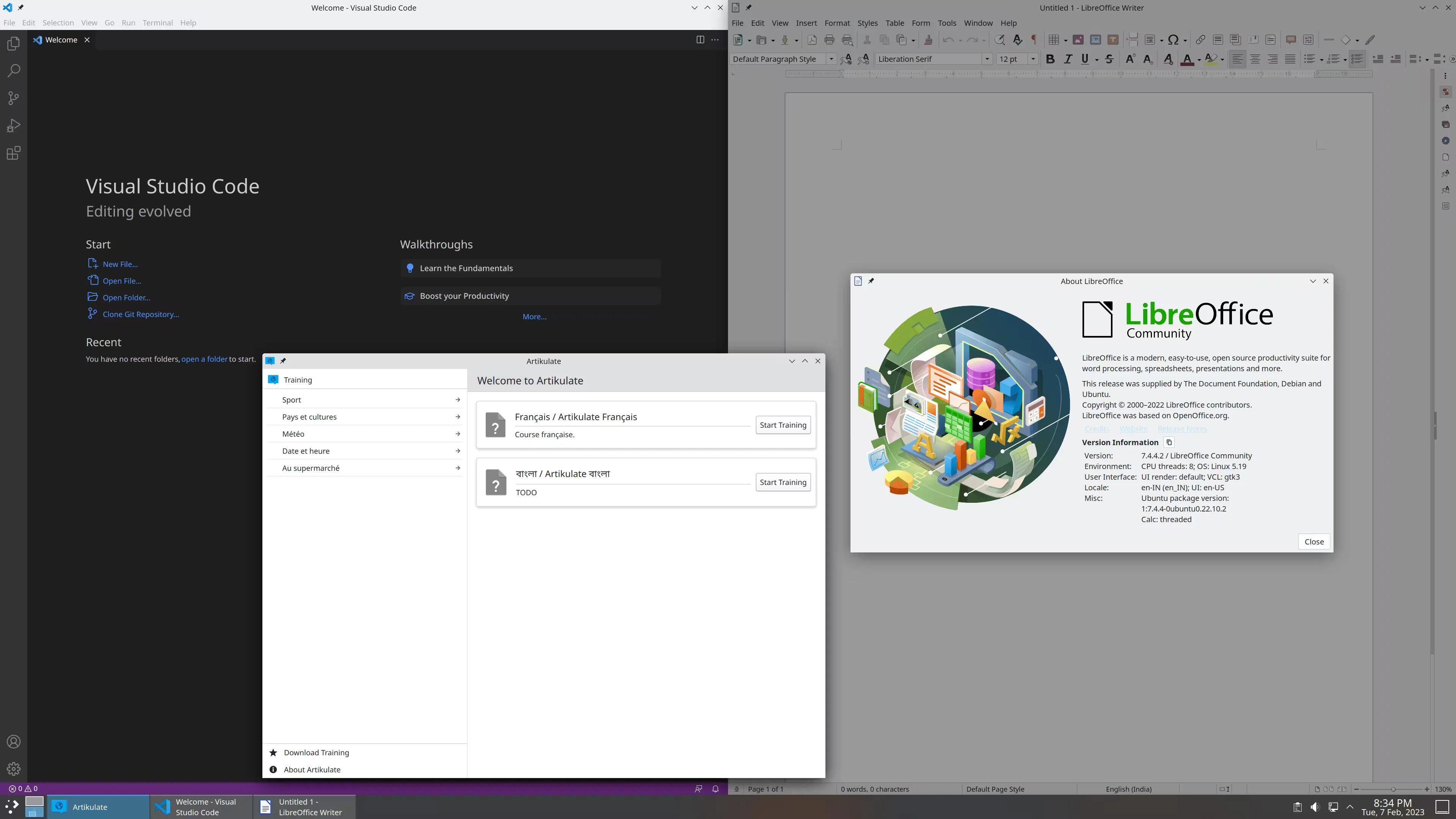
The Benefits of Linux for Students: A Guide to Open-Source Technology in Education
There are many free educational apps available on Linux that are designed for students and have a role to play in the educational system. In this article, we discuss four benefits of it.
-
The Best Tools and Applications for Professional Translators
Translating content to different languages is a time-consuming process that requires high accuracy. Fortunately, there are several tools and applications available to ease a translator’s job.
-

The Best Apps and Tools for Essay Writing on PC
There are many apps and tools available for writing, and we have compiled a list of apps and tools that will help you with your essay writing.
-

The Benefits Of Using Technology In Learning
In this article, we will elaborate on some of the benefits of using technology in learning that can make you ditch the old ways of learning.
-
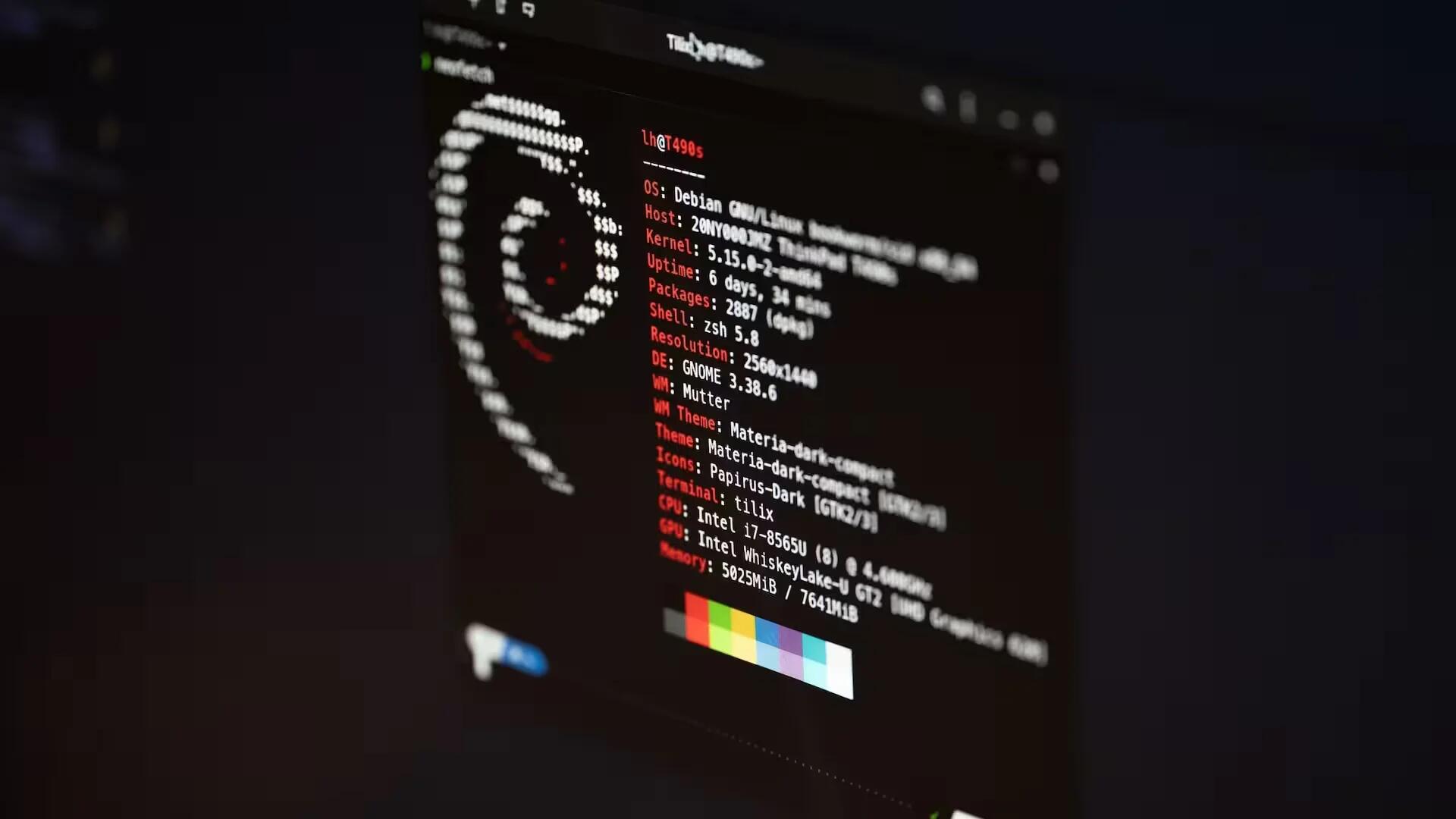
5 Practical Reasons for Learning Linux in 2023
Linux is the driving force behind the majority of the internet, super computers, and multiple devices including smartphones, and learning Linux is clearly one of the most beneficial tasks to consider in 2023.
-

5 Benefits and Uses of Electronic Gadgets in Learning
There are numerous benefits to using electronic gadgets for learning, and we have listed five main benefits you are likely to get if you start using gadgets as part of your learning process.
-

How Digital Technologies Can Help You Overcome Writing Challenges?
Digital tools have proven to be indispensable in academic writing, and let us take a close look at how digital technologies can be used to overcome your writing challenges.
-

How does technology help engage students in the Learning Process?
It is becoming increasingly difficult for students to maintain their attention span for long, and here are 5 of the most effective ways’ we can use technology to help students engage in the learning process.
-
How to Improve Writing Skills with Apps and Gadgets?
When you are attempting to improve your writing skills, you can use various apps to help you pay attention to the written content, grammar, plagiarism, logic, and structure of the written content.
-

How to Use Technologies in Student Projects in 2023?
As schools and classrooms are becoming increasingly digital, it is important to make the technology assist you in your student projects and unfold the best skills that you have!
-

VPN or Proxies: What should you prefer for Gaming
VPN and proxy are two different ways of accessing blocked content. Here we explain the difference between them and why you should pick one over the other.
-

Which Voice-Recording Software Should You Purchase For Your Needs?
here are a number of popular voice recording software are available for to purchase, but before you choose one, here are a few factors you need to consider.
-
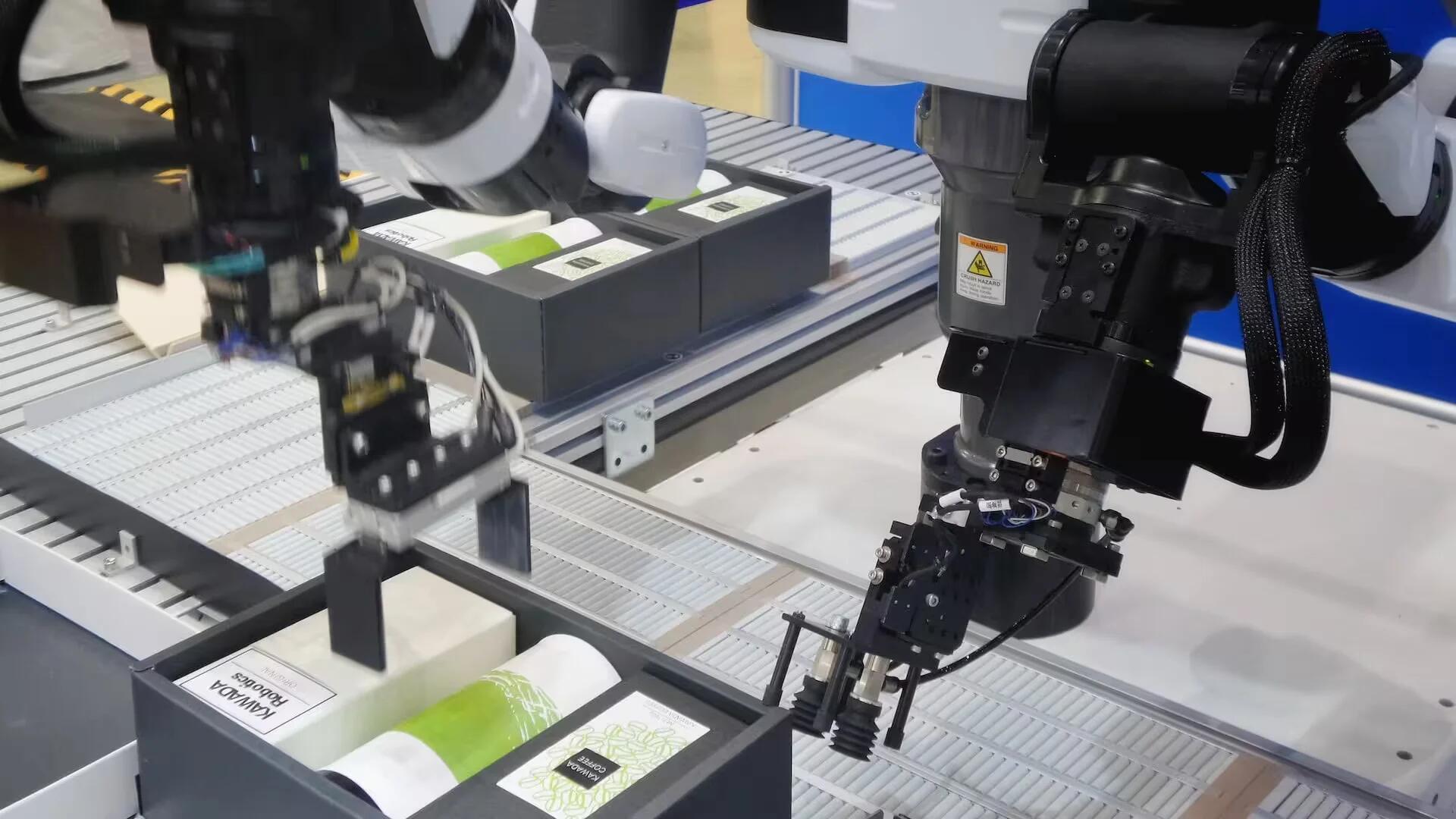
How Robots Can Be Used to Address Unsafe Work Conditions
In this article, we will take a look at a few of the ways in which robots are being used to address unsafe work conditions and remove workers from dangerous spaces.
-
Twitch’s Ban on Gambling Content: What You Need to Know
Twitch has banned gambling live streams on its platform with mixed reviews from Twitch users and here is everything you need to know about the ban.
-
The Role of Data Destruction in Cybersecurity
Below we look at the role of data destruction in cybersecurity and why it should never be taken for granted.
-
What Is Computer Vision in this Modern Time?
Here we will see a brief introduction to computer vision and how it impacts our lives so that we can get a better overview of what is coming up shortly with its presence.