The Importance of Security in Application Development
The mobile app sector is booming, and businesses are starting to realize the many benefits of a custom mobile app for their customers. However, much like a website, a mobile app is a digital platform and is susceptible to hacking by malicious actors.
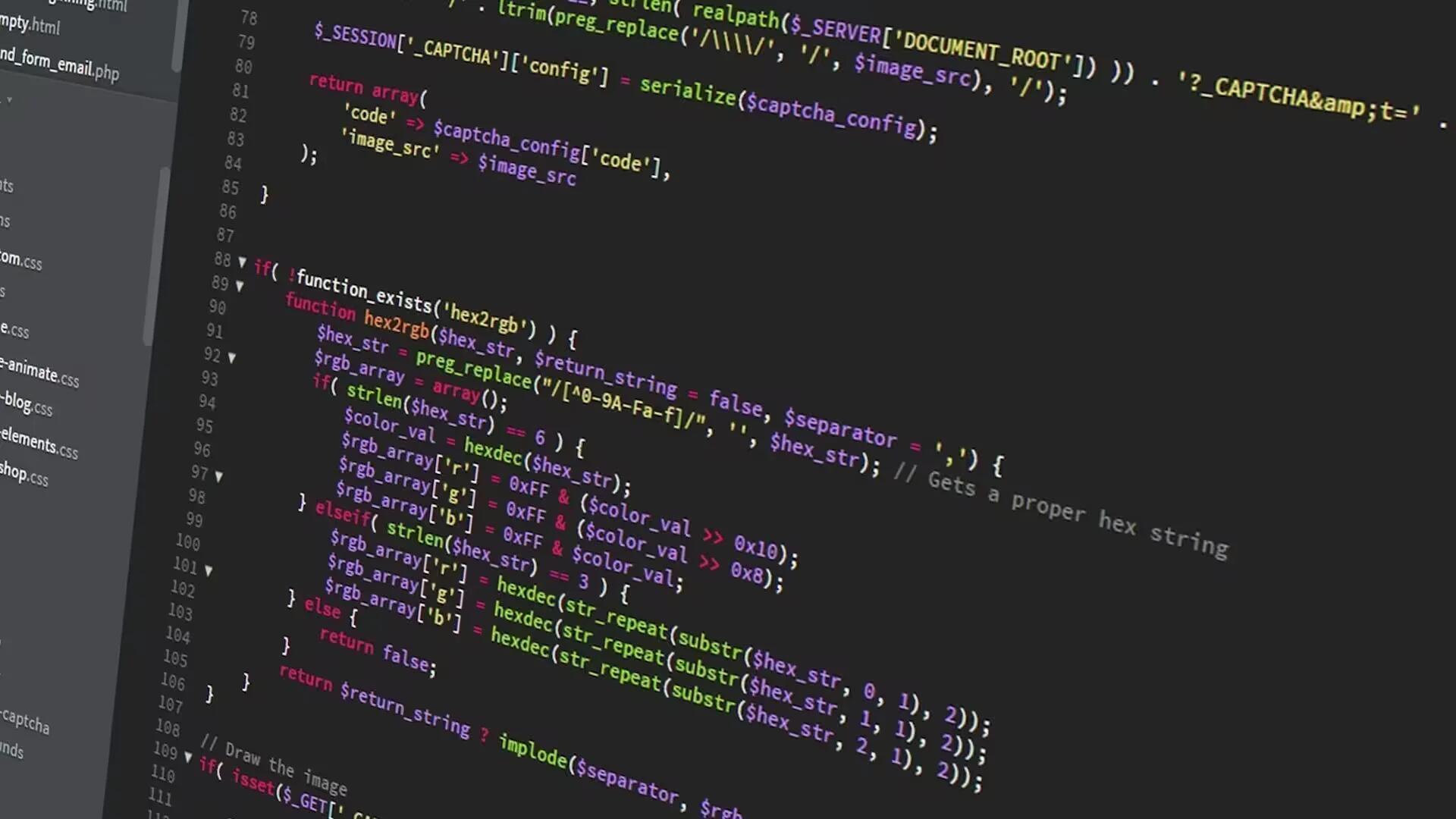
Web hacking
Web hacking is done by tinkering with the web application in various ways and taking control from the end-users. The web application hacker needs to have deep knowledge of the web application architecture to successfully hack it. To be a master, the hacker needs to practice, learn, and also tinker with the application. Multiple strategies like phishing can be effective while adding malicious attachments to an email is another way to infect a PC with a virus that is programmed to do something while avoiding detection; some bad code can disguise itself as something else, moving from folder to folder.
Application hacking
Much like a website, an application can be compromised; with application vulnerability testing, security is assured. There are systems such as Guardrail that do real-time source code scanning to identify and eliminate security bottlenecks. These systems also help developers to avoid bad coding practices that could result in known vulnerabilities like SQL injection, which could lead to clean and readable code. They help developers to build better and more secure software.
Talk to a developer
If you are thinking about creating a mobile app for your business, the next logical step would be an informal Zoom chat, with a software developer. You can outline your concept and the developer can gain information about your business, what it does and how the organization works. Click here for an article on customizable applications, which is an informative read.
Start with a solid foundation
Rather than building the app and looking at cyber-security after the event, the security can be built-in, meaning there are no loopholes for the hacker to discover. Cyber-criminals are extremely resourceful and are always looking for new ways to get the data they need to make some money; built-in security is the best way to prevent a breach.
Penetrative testing
Ethical hackers put their skills to the test by trying to compromise the target app, using all the strategies they know and if they are not successful, you have a secure application. This is the only way to put the app defenses to the test and should the ethical hacker be successful, a security patch can be written and put in place.
Ongoing security
Cybercrime is on the rise and when building an application, you need to incorporate security at the building stage. Once a mobile app has been launched, developers can monitor for issues and bugs and fix them by releasing updates (your customers can set the app to update automatically).
Much like your company website needs constant cyber-monitoring, your mobile app should be under the watchful eye of a cyber-security professional. Should there ever be an attack, the team can trace the origin, and you can report the cyber-attack to the authorities.








 RSS - All Posts
RSS - All Posts