14 iPhone Apps are found communicating with Golduck malware server

Many users consider Apple App Store to be safe and secure. While it is true for most of the time, some questionable apps end up sneaking through the cracks. Recently, Security researchers from Wandera have discovered 14 games that all communicate with the same server used to control Golduck malware for Android. Golduck is an Android-focused malware that infects popular classic game apps.
While the games themselves appeared innocuous, they were loaded with ads. It would have been feasible to use ads to trick users into granting permission for malware installed outside of the App Store, Wandera told TechCrunch. If you have downloaded any of these games, it goes without saying that you need to delete the app now. The list includes:
- Commando Metal: Classic Contra Super Pentron
- Adventure: Super Hard
- Bomber Game: Classic Bomberman
- Super Adventure of Maritron
- Classic Tank vs Super Bomber
- Roy Adventure Troll Game
- Trap Dungeons: Super Adventure
- Bounce Classic Legend
- Block Game
- Classic Bomber: Super Legend
- Brain It On: Stickman Physics
- The Climber Brick
- Chicken Shoot Galaxy Invaders
- Classic Brick – Retro Block
This is especially a concern if you are into the nostalgic side of gaming: These were all retro gaming apps and have been installed over a million times, since being released. That is a lot of potential infections, even if only a fraction of that group taps links to malware. At the time of writing, none of them appear to be available any longer from the U.S. App Store.
Golduck is known for some time as an Android malware that infects games. It was first discovered by Appthority and the malware is found to be infecting classic and retro games on Google Play, by infecting apps with a backdoor code allowing malicious payloads to be pushed to the device. At the time, more than 10 million users were affected by the malware, allowing hackers to run malicious commands at the highest privileges, like sending premium SMS messages from a victim’s phone to make money.
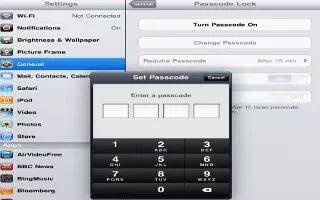
Now, the researchers say iPhone apps linked to the malware could also present a risk. According to the Wandera researchers, the App Store issue is not yet as serious as the Google Play one. The apps are not compromised and do not yet contain malicious code. Currently, the server is just pushing a list of icons in a pocket of ad space in the corner of the app. And when a user opens the game, the server tells the app which icons and links it should serve to that person.
For now, the apps are packed with ads, seemingly to make money. The concern is that this could change: The apps are already communicating with a malicious server and this could open them up to further abuse.
While Apple is typically pretty good when it comes to the security of its App Store, this is a rare example of a lapse on Apple’s part. It is by no means the only one to occur, but typically iOS users are better protected than their Android-using compatriots. Still, it is yet another illustration of why you need to be careful with what you choose to download, even if the store operator is normally good about screening rogue software.