According to a new report, a new iOS malware called KeyRaider has stolen around 225,000 Apple accounts from jailbroken iPhones. This malware was found by the security research company Palo Alto, who claims it as “one of the largest known thefts of its kind”.
The purpose of this attack was to make it possible for users of two iOS jailbreak tweaks to download applications from the official App Store and make in-app purchases without actually paying. The malware has affected over 225,000 users throughout the world, including China, France, Russia, Japan, United Kingdom, United States, Canada, Germany, Australia, Israel, Italy, Spain, Singapore, and South Korea. The KeyRaider malware works through Cydia, the popular app that makes it easier to not only manage installed apps on a jailbroken handset, but also easier to access and install apps not available in the App Store.
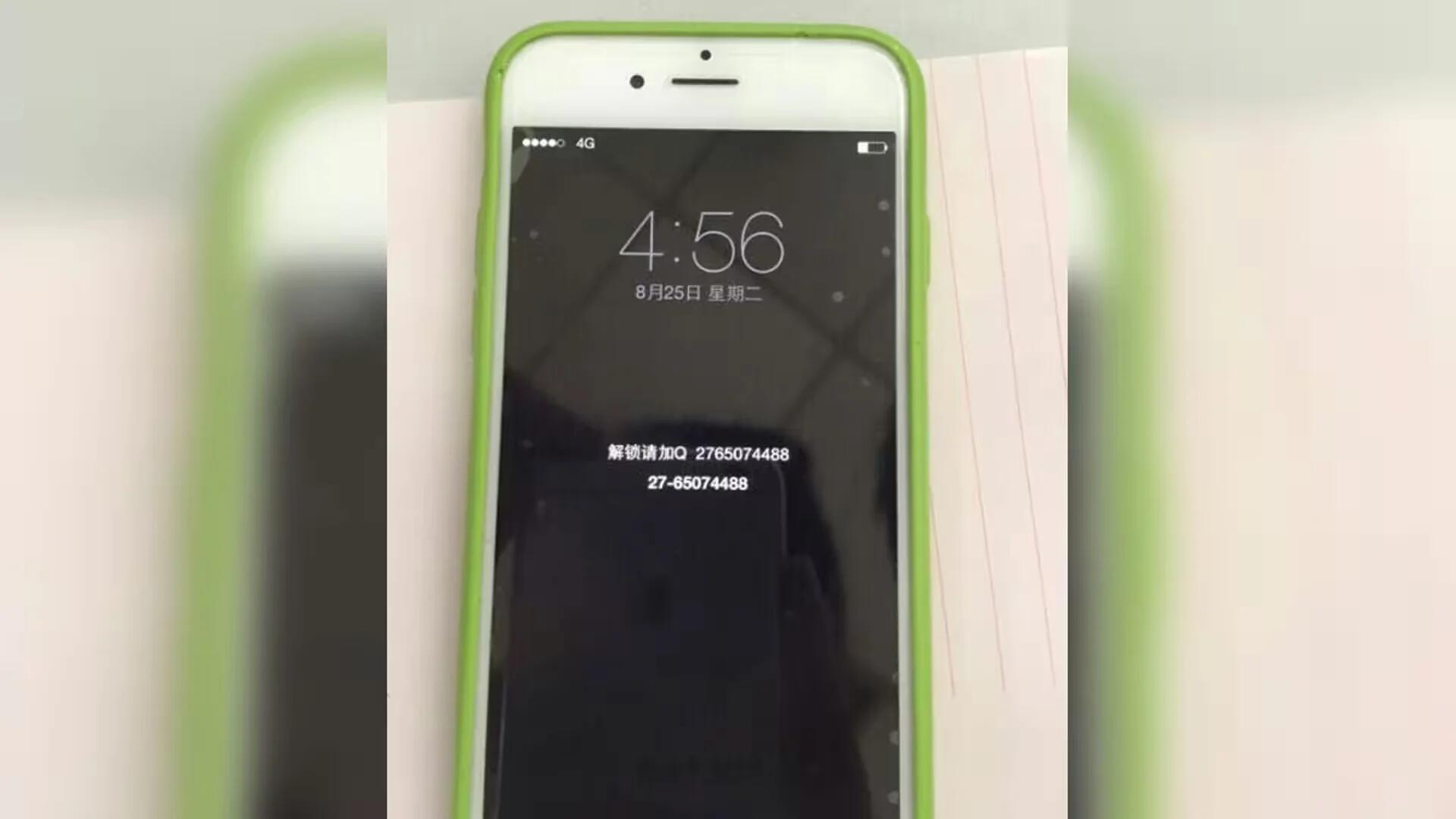
The malware collects a number of other items in addition to Apple ID usernames and passwords. It also targets the device’s unique identifier, or GUID, alongside security certificates and private keys for Apple push notification service as well as App Store purchase data. Once installed, the malware also disables the ability to unlock iOS devices, a feature occasionally used to control your device remotely for ransom.
It can locally disable any kind of unlocking operations, whether the correct passcode or password has been entered. Also, it can send a notification message demanding a ransom directly using the stolen certificate and private key, without going through Apple’s push server. Because of this functionality, some of previously used “rescue” methods are no longer effective.
The purpose of the malware is not only to steal your credentials, but also to allow users to purchase from Apple App Store without paying. It uses stolen credentials to impersonate legitimate users in App Store purchase requests.
To date, the malware records over 20,000 downloads, which means that around that number of users have been abusing the account information of 225,000 stolen credentials.
The malware is more of a concern in China, not only because of the way it was being distributed (through Chinese Cydia repositories), but also because many sellers in the country sell pre-jailbroken iPhones to customers.
According to Palo Alto Networks reports, this malware works only in jailbroken devices, which means your Apple account, is likely fine in case you have not jailbroken any iOS device lately. Even if you have jailbroken your device, the KeyRaider malware needs you to install an app from a third-party Cydia repository, and it is likely many of you have not done that either.
In case you think you might be one of the 225,000 people affected by the hack, you can use this site – WeipTech.org (it is in Chinese, so use Google Translate) to see if your jailbroken device has been compromised.
Source: Palo Alto